- Main
- Computers - Networking
- Black Hat Python: Python Programming...

Black Hat Python: Python Programming for Hackers and Pentesters
Justin Seitz, Tim Arnold你有多喜欢这本书?
下载文件的质量如何?
下载该书,以评价其质量
下载文件的质量如何?
Fully-updated for Python 3, the second edition of this worldwide bestseller (over 100,000 copies sold) explores the stealthier side of programming and brings you all new strategies for your hacking projects.
When it comes to creating powerful and effective hacking tools, Python is the language of choice for most security analysts. In Black Hat Python, 2nd Edition, you’ll explore the darker side of Python’s capabilities—writing network sniffers, stealing email credentials, brute forcing directories, crafting mutation fuzzers, infecting virtual machines, creating stealthy trojans, and more.
The second edition of this bestselling hacking book contains code updated for the latest version of Python 3, as well as new techniques that reflect current industry best practices. You’ll also find expanded explanations of Python libraries such as ctypes, struct, lxml, and BeautifulSoup, and dig deeper into strategies, from splitting bytes to leveraging computer-vision libraries, that you can apply to future hacking projects.
You’ll learn how to:
• Create a trojan command-and-control using GitHub
• Detect sandboxing and automate common malware tasks, like keylogging and screenshotting
• Escalate Windows privileges with creative process control
• Use offensive memory forensics tricks to retrieve password hashes and inject shellcode into a virtual machine
• Extend the popular Burp Suite web-hacking tool
• Abuse Windows COM automation to perform a man-in-the-browser attack
• Exfiltrate data from a network most sneakily
When it comes to offensive security, your ability to create powerful tools on the fly is indispensable. Learn how with the second edition of Black Hat Python.
New to this edition:
All Python code has been updated to cover Python 3 and includes updated libraries used in current Python applications. Additionally, there are more in-depth explanations of the code and the programming techniques have been updated to current, common tactics. Examples of new material that you'll learn include how to sniff network traffic, evade anti-virus software, brute-force web applications, and set up a command-and-control (C2) system using GitHub.
When it comes to creating powerful and effective hacking tools, Python is the language of choice for most security analysts. In Black Hat Python, 2nd Edition, you’ll explore the darker side of Python’s capabilities—writing network sniffers, stealing email credentials, brute forcing directories, crafting mutation fuzzers, infecting virtual machines, creating stealthy trojans, and more.
The second edition of this bestselling hacking book contains code updated for the latest version of Python 3, as well as new techniques that reflect current industry best practices. You’ll also find expanded explanations of Python libraries such as ctypes, struct, lxml, and BeautifulSoup, and dig deeper into strategies, from splitting bytes to leveraging computer-vision libraries, that you can apply to future hacking projects.
You’ll learn how to:
• Create a trojan command-and-control using GitHub
• Detect sandboxing and automate common malware tasks, like keylogging and screenshotting
• Escalate Windows privileges with creative process control
• Use offensive memory forensics tricks to retrieve password hashes and inject shellcode into a virtual machine
• Extend the popular Burp Suite web-hacking tool
• Abuse Windows COM automation to perform a man-in-the-browser attack
• Exfiltrate data from a network most sneakily
When it comes to offensive security, your ability to create powerful tools on the fly is indispensable. Learn how with the second edition of Black Hat Python.
New to this edition:
All Python code has been updated to cover Python 3 and includes updated libraries used in current Python applications. Additionally, there are more in-depth explanations of the code and the programming techniques have been updated to current, common tactics. Examples of new material that you'll learn include how to sniff network traffic, evade anti-virus software, brute-force web applications, and set up a command-and-control (C2) system using GitHub.
年:
2021
出版:
2
出版社:
No Starch Press
语言:
english
页:
216
ISBN 10:
1718501137
ISBN 13:
9781718501133
文件:
PDF, 13.65 MB
您的标签:
IPFS:
CID , CID Blake2b
english, 2021
在1-5分钟内,文件将被发送到您的电子邮件。
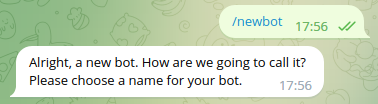
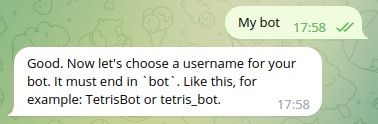
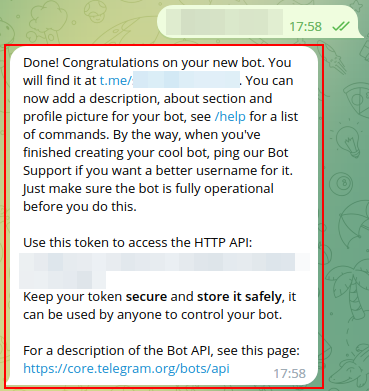
该文件将通过电报信使发送给您。 您最多可能需要 1-5 分钟才能收到它。
注意:确保您已将您的帐户链接到 Z-Library Telegram 机器人。
该文件将发送到您的 Kindle 帐户。 您最多可能需要 1-5 分钟才能收到它。
请注意:您需要验证要发送到Kindle的每本书。检查您的邮箱中是否有来自亚马逊Kindle的验证电子邮件。
正在转换
转换为 失败
关键词
关联书单
















































































































































 Amazon
Amazon  Barnes & Noble
Barnes & Noble  Bookshop.org
Bookshop.org  转换文件
转换文件 更多搜索结果
更多搜索结果 其他特权
其他特权